Please note that the only procedures supported and maintained by Centreon are those published in the official documentation. If you have a question about this article, post it in the comments.
In this article we will implement authentication based on the SAMLv2 protocol to connect your users to the Centreon web interface. This authentication will be performed by the Apache web server and will use Centreon's Web SSO functionality.
Prerequisites
Centreon does not manage the import of users via the Web SSO functionality. Users must therefore be previously declared in Centreon via the Configuration > Users > Contacts / Users menu.
In addition, Centreon must be accessible through HTTPS with a valid certificate and a DNS record.
This tutorial was made with the Centreon 22.04.x version, installed on the CentOS 7 operating system. The dependencies are PHP in version 8.0 and Apache in version 2.4 (httpd24-httpd).
Moreover, you must have access to the configuration of your identity provider to add a new application and configure it.
Configure the Apache web server
Install mod_auth_mellon Apache extension
yum install -y httpd24-mod_auth_mellon httpd24-mod_ssl openssl xmlsec1-openssl xmlsec1
Create a directory to store metadata
mkdir -p /opt/rh/httpd24/root/etc/httpd/saml2
Configure Apache to use SAMLv2 for authentication
Edit /opt/rh/httpd24/root/etc/httpd/conf.d/10-centreon.conf file.
After the following lines:
Alias /centreon/api /usr/share/centreon
Alias /centreon /usr/share/centreon/www/
Add:
<Location />
MellonEnable info
MellonEndpointPath /mellon/
MellonSPMetadataFile /opt/rh/httpd24/root/etc/httpd/saml2/mellon_metadata.xml
MellonSPPrivateKeyFile /opt/rh/httpd24/root/etc/httpd/saml2/mellon.key
MellonSPCertFile /opt/rh/httpd24/root/etc/httpd/saml2/mellon.crt
MellonIdPMetadataFile /opt/rh/httpd24/root/etc/httpd/saml2/idp_metadata.xml
MellonIdP <IDP ADDRESS>
MellonMergeEnvVars On
</Location>
Replace <IDP ADDRESS> by the endpoint to access to your IDP.
For example, if you will use Keycloak as IDP and Centreon_SSO as realm, you will have:
MellonIdP http://<IP>:8080/auth/realms/Centreon_SSO
Then add the following block:
<Location /centreon>
AuthType Mellon
MellonEnable auth
Require valid-user
</Location>
Configure metadata exchanges between Centreon and the identity provider
Configure Apache metadata
Execute following commands:
cd /tmp
fqdn=`hostname`
mellon_endpoint_url="https://${fqdn}/mellon"
mellon_entity_id="${mellon_endpoint_url}/metadata"
file_prefix="$(echo "$mellon_entity_id" | sed 's/[^A-Za-z.]/_/g' | sed 's/__*/_/g')"
/opt/rh/httpd24/root/usr/libexec/mod_auth_mellon/mellon_create_metadata.sh $mellon_entity_id $mellon_endpoint_url
mv ${file_prefix}.cert /opt/rh/httpd24/root/etc/httpd/saml2/mellon.crt
mv ${file_prefix}.key /opt/rh/httpd24/root/etc/httpd/saml2/mellon.key
mv ${file_prefix}.xml /opt/rh/httpd24/root/etc/httpd/saml2/mellon_metadata.xml
Configure Centreon on your IdP
Configure your Identity Provider to add the Mellon Service Provider (Centreon)
The XML metadata is located on the Centreon Server in this file: /opt/rh/httpd24/root/etc/httpd/saml2/mellon_metadata.xml
Then download your Identity Provider metadata and store it in the /opt/rh/httpd24/root/etc/httpd/saml2/idp_metadata.xml file on your Centreon server.
For example, from Keycloak IDP:
curl -k -o /opt/rh/httpd24/root/etc/httpd/saml2/idp_metadata.xml http://<IDP_IP>:<IDP_NAME>/auth/realms/<realm_name>/protocol/saml/descriptor
Configure Centreon
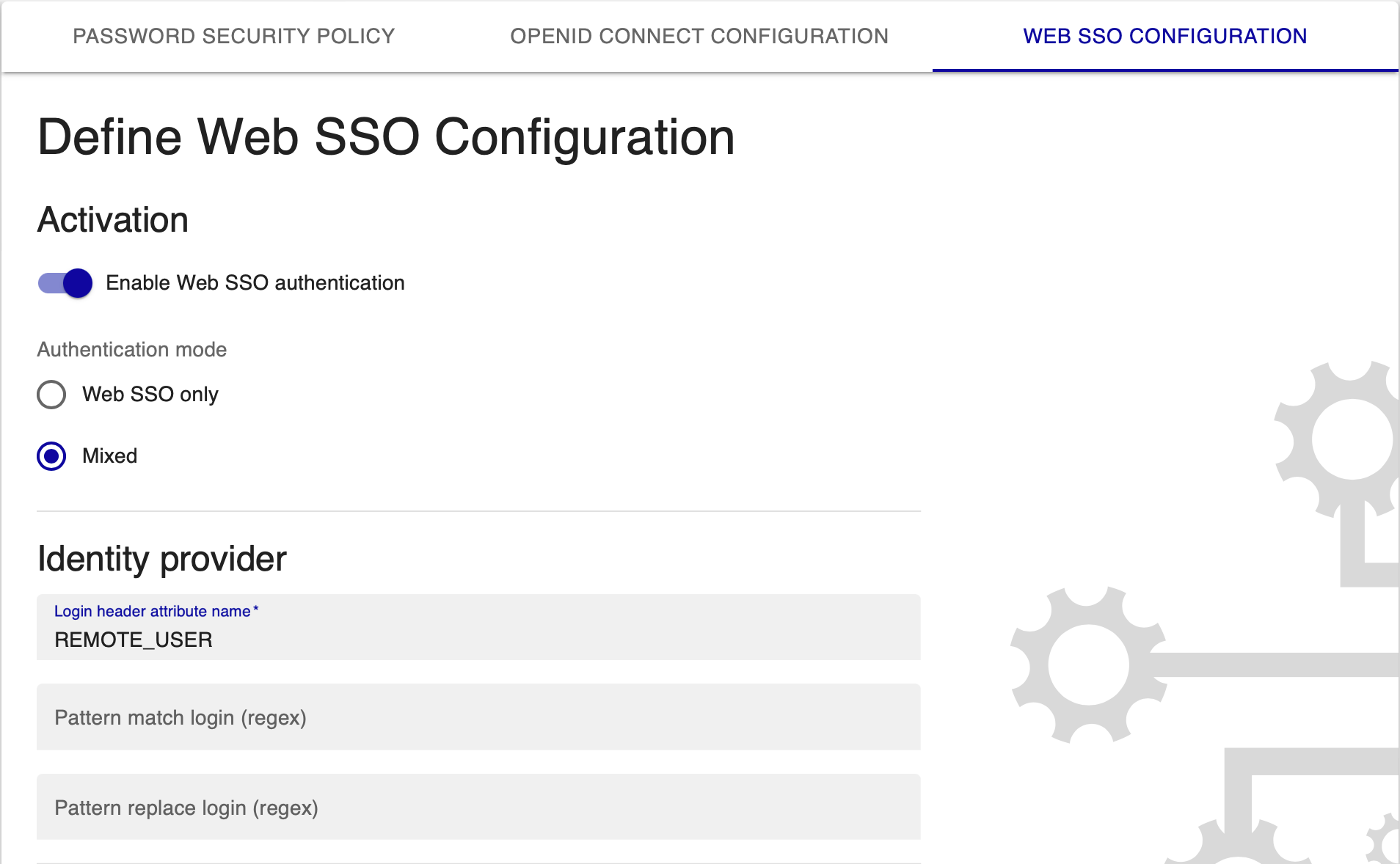
With an admin account, go to the Administration > Authentication menu and go to Define Web SSO Configuration tab:
- Enable SSO authentication
- Choose Mixed for Authentication mode
- Define REMOTE_USER for Login header attribute name
Test your Apache configuration:
/opt/rh/httpd24/root/usr/sbin/apachectl -t
Then Restart Apache:
systemctl restart httpd24-httpd
You can now access to http(s)://<IP_CENTREON>/centreon and authenticate with your IDP.
